Earlier this week we learned something horrible, although totally predictable: In the vast majority of circumstances, the FBI does not obtain judicial warrants to deploy controversial stingray technology against the public. Amazingly, the government justifies this patently illegal position by asserting—once again—that cell phone users have no right to privacy in public spaces. (I assume the FBI would take a different position if police accountability activists deployed wifi sniffers or stingrays at the police, even if they did so in public parks.)
I’ve long assumed that the FBI and even state and local police use cell site simulators to keep track of protesters at political events. We know for a fact that police departments are using the powerful spy tools to find drug dealers, despite their promises to use the technology principally in serious terrorism cases.
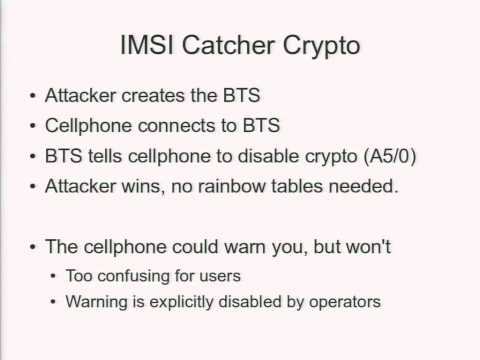
How can you protect yourself against these IMSI catchers? First off, read about exactly how they work. To protect your privacy, the simplest thing you can do is install a few apps on your smartphone, to shield the content of your communications from FBI or police capture. It’s a pretty safe bet that both Signal (for the iPhone) and Redphone (for Android) defeat the IMSI catcher’s wiretap capabilities. For texting and chat, you can use TextSecure and ChatSecure to achieve the same.
Nathan Freitas of the Guardian Project explains it to me in an email:
As far as I know, IMSI catchers don't currently have the ability to
break the encryption used in those apps, or TextSecure, ChatSecure, etc…I think in most cases, the stingray won't support 3G/4G networks, so the data connection will just drop, and the apps won't work. TextSecure will failover to SMS though, and if you aren't sending encrypted messages, those can be intercepted.
If the stingray DOES support 3G/4G, then it might attempt to
man-in-the-middle the connection and/or log all the packets it sees. Redphone/Signal, etc, would detect/stop the MiTM attack.
That’s great news for activists, who need to be able to securely communicate at protests. But using these apps won’t stop the cops or the FBI from identifying your phone, and therefore placing you at the protest. They also won’t stop the cops or FBI from wiretapping your email, Twitter, or other unencrypted data transfers from your phone. Finally, these encrypted communications apps won’t notify you if there’s a stingray around to be worried about in the first place.
Enter two other apps: SnoopSnitch and Android IMSI-Catcher Detector, both for Android. Neither app can stop the cops from connecting with your handset, but they might be able to alert you to the presence of a stingray in your vicinity. Check out those links to learn more about the projects.
There is a non-technical way around stingray surveillance, of course: Leave your phone at home. Alternatively, if you want to live tweet the protest but don't want to take the risk that cops will dig around your phone while your signal bar spins, get yourself a burner smartphone just for protests. Load it up with the Twitter app, an IMSI detector app, and some encrypted communications tools, and leave the rest of your life off of it.
